WordPress powers a remarkable one-1/3 of all websites these days. It has been the CMS platform of preference for our community because of the mid-aughts when many of WordPress’s search engine optimization capabilities have been carried out.
It is relentlessly attacked, largely for search engine optimization junk mail motives, but attacks can worsen. Here’s an observation of some WordPress basics and ways to secure your WordPress web page.
Is WordPress safe?
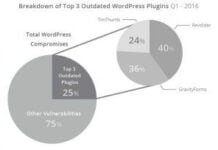
The state-of-the-art model of WordPress is very secure out of the field. Neglecting to update it, however, amongst other things, could make it risky. This is why many protection specialists and builders aren’t WordPress enthusiasts. WordPress also resembles PHP spaghetti, which is inherently insecure code; WordPress warns that vulnerabilities “stem from the platform’s extensible elements, particularly plugins and issues.”WordPress updates
There is no such thing as a one hundred percent cozy system. WordPress desires protection updates to function accurately, and people updates shouldn’t negatively affect you. Turn on computerized protection updates. Updating the WordPress center requires ensuring the whole lot is well-matched. Update plugins and themes as soon as well-matched versions are to be had.
 Open supply
Open supply
WordPress is open supply, which includes dangers and benefits—the mission blessings from a developer network that contributes code for the middle. The middle group patches safety flaws observed using the community, even as hooligans learn how to pry matters open. Vulnerabilities are scripted into scans by exploit applications that may stumble on what variations of things are running to suit acknowledged flaws for your versions.
Protect yourself first.
You can do things to guard yourself even if you don’t have an administrator function. Ensure you’re running in a comfortable community with a regularly scanned workstation. Block ads to prevent sophisticated attacks that masquerade as images. Use VPN for quit-to-quit encryption whenever you’re running at public WiFi hotspots to save you from session hijacking and MITM assaults.
Secure Passwords
Securely coping with passwords is critical, irrespective of what function you have. Make certain your password is particular and long enough. Combinations of numbers and letters are not secure, despite punctuation, while passwords aren’t long enough. It would help if you had lengthy passwords. Use phrases of 4 or 5 words strung very if you want to memorize, but it’s better to usingervisor that generates passwords for you.
Password Peri is higher.
Why is length so essential? In this manner, eight-person passwords crack in less than 2.5 hours using a loose and open supply application called HashCat. It doesn’t count how unintelligible your password is; it simply takes hours to crack short passwords. Starting at 13+ characters, cracking starts offevolved to get insurmountable, at least for now.
Administrators
If you have an admin consumer role, create a new person for yourself restricted to an editor role. Begin using the new profile instead of the admin. In that manner, extensive location internet assaults may be targeted at attacking your editor position credentials. If your consultation is hijacked, you have the admin potential to trade passwords and wrest manipulation far from the intruders. Compel all and sundry, possibly via a plugin, to comply with the robust password policy.
Security coverage
If you are concerned about safety, carry out code audits of your plugins and themes (glaringly). Establish the principle of least privilege for all users. This will force hackers to perform shell-popping hints and privilege escalation, which entails attacking objectives apart from WordPress credentials.
Change report permissions
If you control the host, offer yourself an SFTP account through the Control Panel’s usage if you have one, or strive to determine what administrator user interface you’ve got access to. It may have the side impact of configuring credentials to open a relaxed shell terminal window (SSH). That way, you may perform additional security features, the use of system utilities, and more.
Lockdown important documents
Some documents must never be accessed except through the PHP system jogging WordPress. You can change report permissions and edit them. Htaccess document to lock those files down further. To other record permissions, use your SFTP consumer (if it has the choice) or open a terminal shell window and run the chmod application command.

 Open supply
Open supply