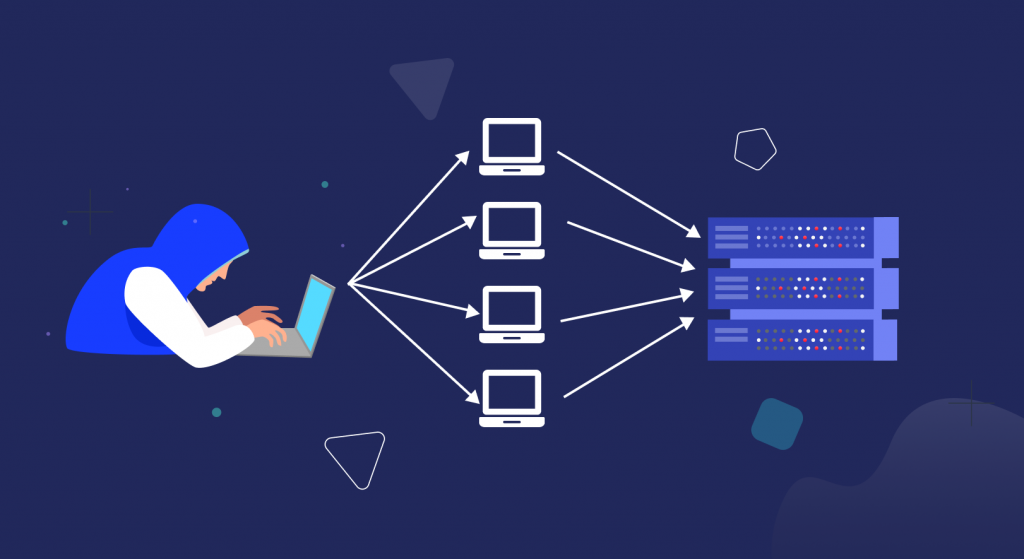
A newly observed piece of malware concentrated on net servers strolling on Linux machines is scanning famous content material management structures (CMS) for vulnerabilities to extend a botnet. Russian security firm Dr. net says the malware is capable of launching allotted denial of carrier (DDoS) assaults, sending spam e-mails, and self-propagating across a network. The malware goals several broadly used structures, consisting of Drupal, WordPress, Magento, ContactScanner, AirOS, Exagrid, Jetspeed, and others.
One malware feature scans for websites that use these systems, attempting to exploit recognized vulnerabilities to show personal information, non-public SSH keys, and login credentials saved on remote servers. The safety firm attributes the malware to recent attacks on Drupal websites that used an Sq. Injection flaw to compromise net servers. Victims faced a demand of 1.4 Bitcoin to release the key. As networks evolve, visibility stays key to managing IT security hazards in commercial enterprise terms.
More from Gigamon
In keeping with Dr. Net, the malware’s DDoS function produces email spam with a message purportedly written by the Armada Collective — a name co-opted using online crook companies hoping to capitalize on excessive profile attacks attributed to the crowd. Armada Collective became blamed for a chain of assaults in the final year on Swiss ISPs and Switzerland-based comfy email company ProtonMail, which, against the commonplace recommendation, paid a ransom and became struck by using attackers besides.
RELATED ARTICLES :
- Top 5 eBook Apps for Android
- 15+ Tips for Buying the Perfect WordPress Theme
- iPad 2 – New and Updated Review
- Language apps for iOS: Rosetta Stone beats Duolingo and Babbel
- four Pinterest Widgets for WordPress
But, content material distribution community issuer CloudFlare is closing yr known as out scammers for using the Armada Collective call to bluff Sufferers into paying up when threatened with a DDoS assault. The firm stated that no longer a single assault had resulted from a danger. Recipients of email unsolicited mail from this botnet will see a message claiming to be either from the Armada Collective or Anonymous, which both contain the identical chance. “If you record this to media and attempt to get a few unfastened publicity by using our name, in preference to paying, the attack will start completely and last for a long time. This isn’t a joke. Our assaults are extremely powerful – sometimes, over 1 Tbps per 2d. So, no cheap protection will assist,” the message reads.